When creating new software and applications, it’s tempting to manage everything the way you personally would prefer, and not the way your users would prefer. Maybe you’ve never personally been hacked, and so you’re not certain why everyone’s so adamant about hiring security analysts and researchers (can’t everyone just think like you?). Or maybe you were hacked once years ago, and you figure it’s not a big deal anymore.
Two things. Regardless of if you’ve ever been hacked, if your application is widely successful then at least some of your future users will have been — you’ll now have to protect them as best you can while fostering trust (making these users feel sufficiently safe when using your app). And if you haven’t yet been hacked, count your blessings; according to some estimates 64% of businesses have already suffered a cyber-attack, and this percentage will only rise over time. The solution lies in hiring the right IT security architects, seasoned professionals who can create and maintain a safe, strong digital infrastructure for you.

While striving for a feeling of security isn’t always how to attain actual security, our security analyst jobs do let you have your cake and eat it too. We’re happy to provide you with experienced cyber security consultants who can join your team working hybrid-style!
If your team is already working together from afar, don’t reinvent the wheel on our account! Our security architects are consummate professionals, comfortable in remote-first organizations and ready to help you safeguard mission critical data.
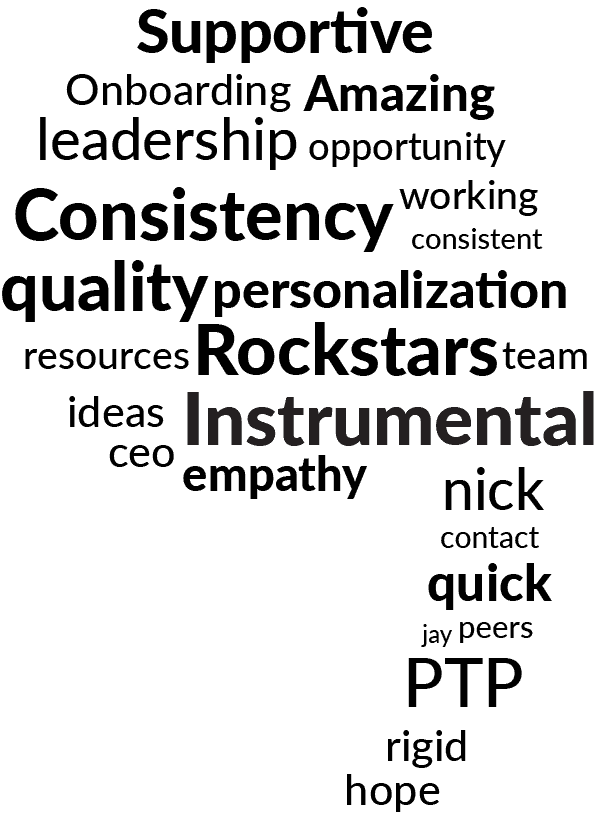
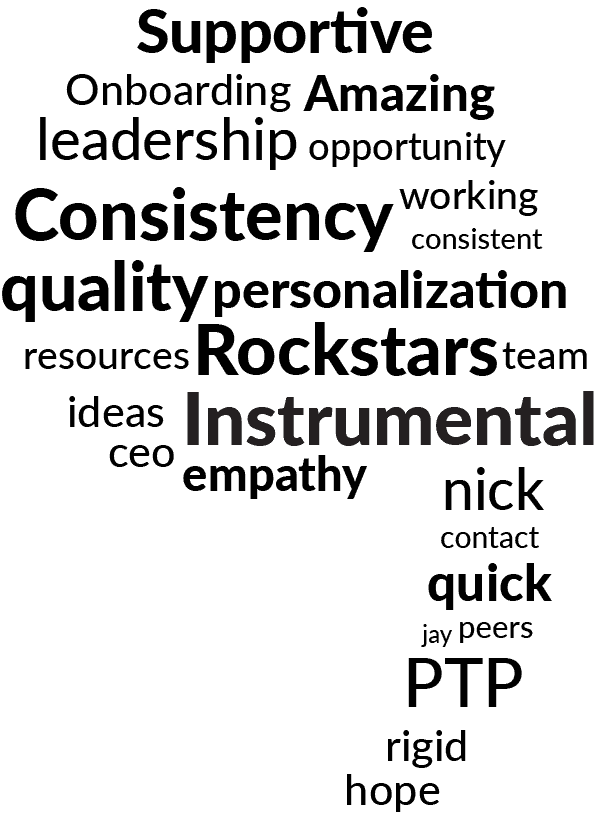
Build a high-performing security team with PTP’s talent pool. Recruit top Security Analysts from nearby regions to leverage shared cultural understanding, seamless real-time collaboration, and an optimized budget.
While striving for a feeling of security isn’t always how to attain actual security, our security analyst jobs do let you have your cake and eat it too. We’re happy to provide you with experienced cyber security consultants who can join your team working hybrid-style!
If your team is already working together from afar, don’t reinvent the wheel on our account! Our security architects are consummate professionals, comfortable in remote-first organizations and ready to help you safeguard mission critical data.
Build a high-performing security team with PTP’s talent pool. Recruit top Security Analysts from nearby regions to leverage shared cultural understanding, seamless real-time collaboration, and an optimized budget.


Hire skilled contractors on a fixed-term basis.

Hire top talent, initially as consultants on our payroll, and eventually transitioning into contracted employees.

Hire talent from nearshore destinations to optimize operational costs while maintaining cultural, linguistic, and temporal parity

Hire best-in-class talent on a permanent basis to fulfil your organization’s requirements.
Access highly-skilled talent from around the globe for
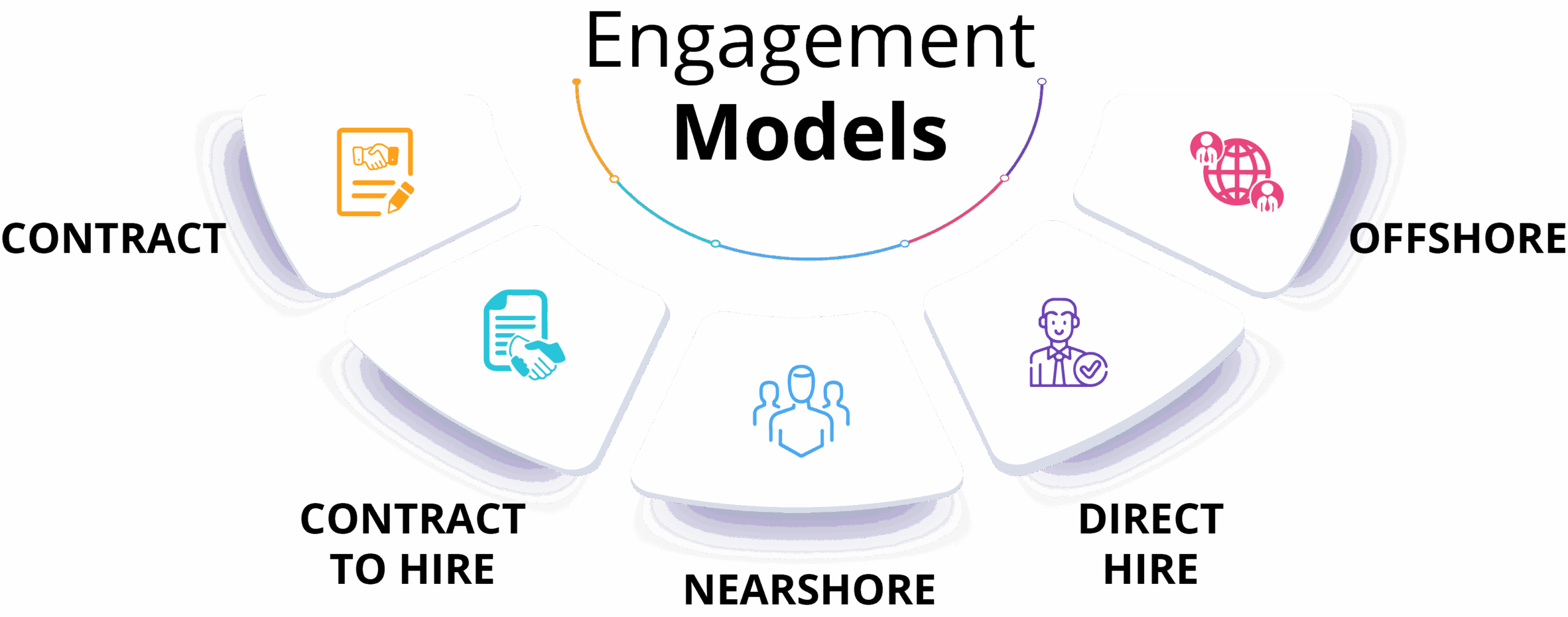
Hire skilled contractors on a fixed-term basis.

Hire top talent, initially as consultants on our payroll, and eventually transitioning into contracted employees.
Hire talent from nearshore destinations to optimize operational costs while maintaining cultural, linguistic, and temporal parity.
Hire best-in-class talent on a permanent basis to fulfil your organization’s requirements.
Access highly-skilled talent from around the globe for.


Hire skilled contractors on a fixed-term basis.

Hire top talent, initially as consultants on our payroll, and eventually transitioning into contracted employees.

Hire talent from nearshore destinations to optimize operational costs while maintaining cultural, linguistic, and temporal parity.

Hire best-in-class talent on a permanent basis to fulfil your organization’s requirements.

Access highly-skilled talent from around the globe for.
1. Get in touch : Fill out this form to let us know your cyber security hiring needs.
2. Connect with experts : One of our expert recruiters will reach out to discuss your unique requirements.
3. Candidate assessment : Sit back and relax as our dedicated recruiting team taps into our expansive talent pool and uses our proprietary 5-Step Process to identify the best candidates for your needs.
4. Interview best-in-class talent : We arrange for you to interview highly qualified talent, picked for their technical aptitude, soft skills, and culture fit.
5. Start working : Once the contract is signed, we’ll guide the new hire through our streamlined and holistic onboarding program, so they can hit the ground running!

Delivering 25 years of excellence in the tech recruiting space, our recruiters are some of the most knowledgeable in the industry. Every day we place candidates where they’re able to make an immediate impact on your business.
Our recruiters make it a goal to find the best and brightest candidates worldwide. Whether you need to hire senior security analysts located nearby, or a few junior security researchers to work remotely, we’ve got the perfect match.
Don’t waste time copying and pasting job descriptions across cookie-cutter job sites! When you hire through PTP, any opportunities you provide us will automatically be posted to our job listings page, and any other sites you direct.
To truly keep current in our increasingly connected, hyper-digital world, you need to hire cyber security architects who don’t miss a trick. Our recruiters are just as on the ball — they can provide you with a short list of well-qualified candidates within days of learning your requirements.
Nobody wants to write job descriptions all day. But everyone needs to hire new team members sometime! Let us provide you with human-written, data-driven job descriptions to capture candidates’ attention and drive applicants to your door.

1.
Fill out this form to let us know your cyber security hiring needs.
2.
3.
Sit back and relax as our dedicated recruiting team taps into our expansive talent pool and uses our proprietary 5-Step Process to identify the best candidates for your needs.
4.
We arrange for you to interview highly qualified talent, picked for their technical aptitude, soft skills, and culture fit.
5.
Once the contract is signed, we’ll guide the new hire through our streamlined and holistic onboarding program, so they can hit the ground running!
Your organization’s computer systems and networks need protection from increasingly complex cyberattacks. Fill out the form below, and PTP will match you with cybersecurity analysts to protect stakeholders from attacks before they happen.
Information security analyst jobs are hyper-strategic positions located at the heart of your company’s defense systems, so it’s imperative that you find the right candidate/s immediately when vacancies crop up. These experts will be responsible for the majority of the organization’s security system, and you’ll also want them to codify an emergency response plan in case of a true cyber-attack. To provide an optimal defense, a senior security analyst needs to be up to date on the current threat landscape at all times – but how can you be certain, when all you see is a resume? Here are a few more duties common to security analyst jobs – you can save this list and refer back when creating job descriptions:
Hiring security architects from PTP is easy! Just fill out the form below with your contact information, and a PTP recruiting specialist will reach out to start the process. They’ll zero in on you and your business’ needs, craft job listings to your exact specifications, promote the job posting, help you screen for interviews, and much more.
IT security analyst jobs are very demanding roles, and when hiring you want to be sure that your chosen candidates are up to the challenge of the position. This can be difficult when you are not yourself a cyber security analyst, and when you have just a resume to review — for your reference, here is a list of the basic qualifications you’ll want to look for when hiring for security analyst jobs:
Hiring experienced cyber security architects is a tough job, but if you want to deliver on the full promise of your company’s software development efforts, it has to be done. While you can hire without the help of a trusted, experienced partner, why take the chance? PTP’s professional recruitment specialists take the time to understand your team’s toughest challenges and to match you with a security consultant who’s the best fit for your needs.
Yes, nearshore Security Analysts can be hired for various project durations. Whether you need short-term expertise for a specific task or long-term support for ongoing security management, nearshore Security Analysts at PTP offer flexible engagement models. This adaptability allows you to meet your project’s exact requirements and timelines, ensuring you have the right security expertise exactly when needed.
©2026 Peterson Technology Partners